Preemptive cybersecurity
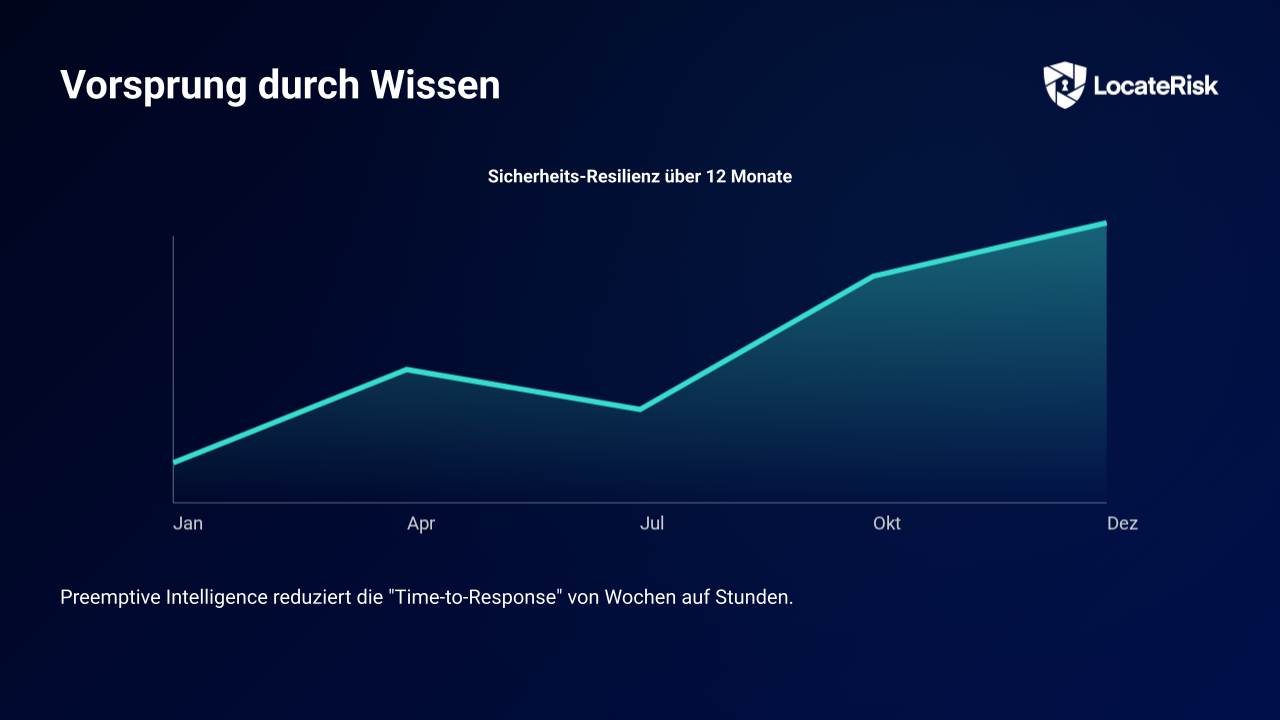
Minimization of time-to-detection through preemptive intelligence
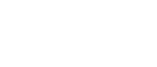
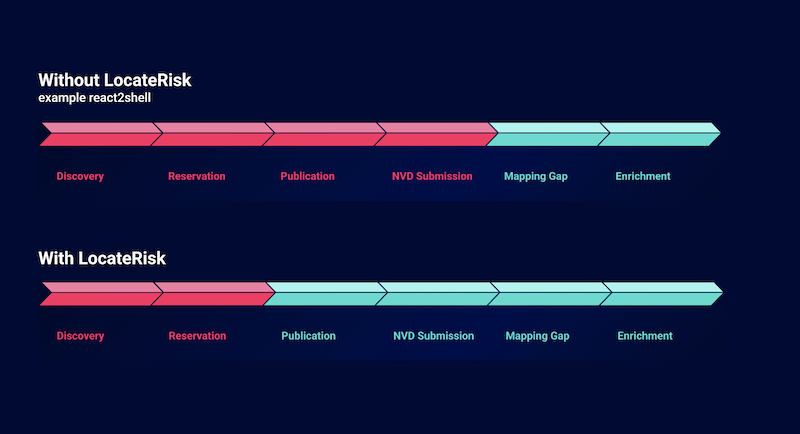
LocateRisk uses Preemptive Intelligence for faster risk assessment and is therefore independent of US data sources such as the National Vulnerability Database (NVD). This means that critical gaps can be closed even before the official NVD analysis. The result: verifiable security with reduced risk management effort: Made in Germany, EU-hosted and NIS2-compliant.