CVE-2025-12686: Critical vulnerability in Synology BeeStation (CVSS 9.8)
Analysis of the critical vulnerability CVE-2025-12686 (CVSS 9.8) in Synology BeeStation, which allows unauthenticated remote code execution. Details and measures.
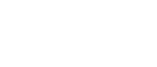
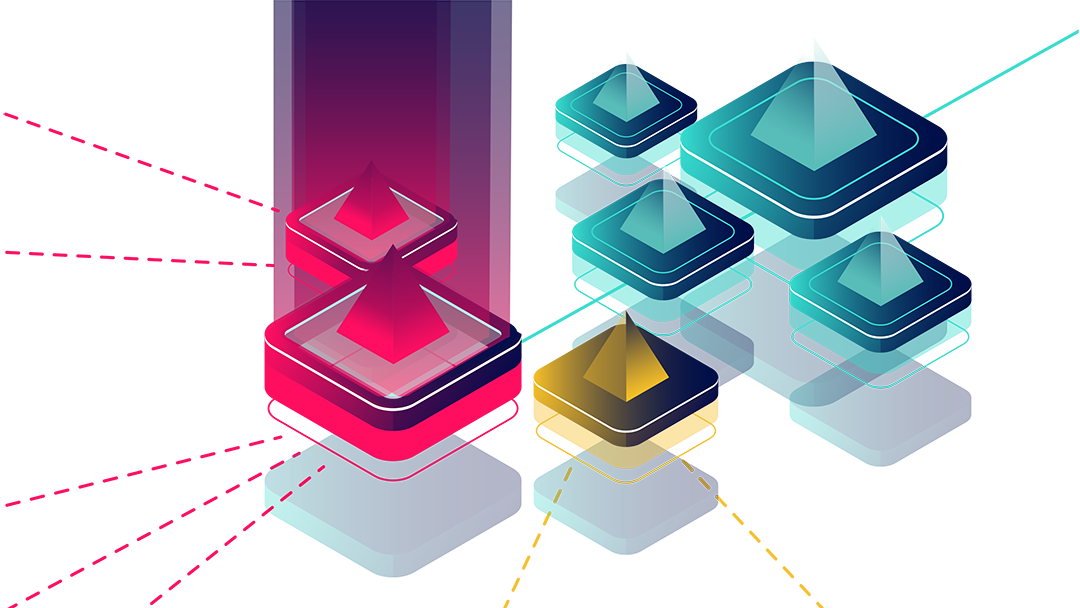
Eliminate shadow IT with LocateRisk MCP & AI | EASM
The identification of unknown infrastructure is a core task in External Attack Surface Management (EASM). LocateRisk provides a specialized interface based on the Model Context Protocol (MCP) for this purpose. LocateRisk is currently the only provider to enable direct machine-to-machine communication, which makes complex detection paths of IT systems immediately analyzable for artificial intelligence.

Cyberattack on Foxconn: A stress test for vendor risk management of global supply chains
What happened? Facts and allegations According to reports, there were IT disruptions from May 1, 2026, primarily affecting the plant in Mount Pleasant, Wisconsin - an important center for the production of AI servers. On May 11, Foxconn appeared on the Nitrogen Group's leak site. The attackers threatened to release over 11 million [...]

BSI C3A: Cloud sovereignty & operational independence
The BSI has presented a list of criteria that defines when a cloud service is considered sovereign. The focus is on data control options, transparency of the service provider and the ability to comply with regulatory requirements.

Lukas Baumann in the CIO Views Magazine Portrait
Making the invisible visible - that's what drives us at LocateRisk GmbH. Lukas Baumann in the CIO Views Magazine Portrait.
AI-native safety analysis
LocateRisk provides an interface based on the Model Context Protocol (MCP). LocateRisk is currently the only provider in the field of External Attack Surface Management (EASM) and Cyber Vendor Risk Management (C-VRM) to enable direct machine-to-machine communication. The technology combines security analyses directly with artificial intelligence, making complex data available for automated decisions without any loss of time.

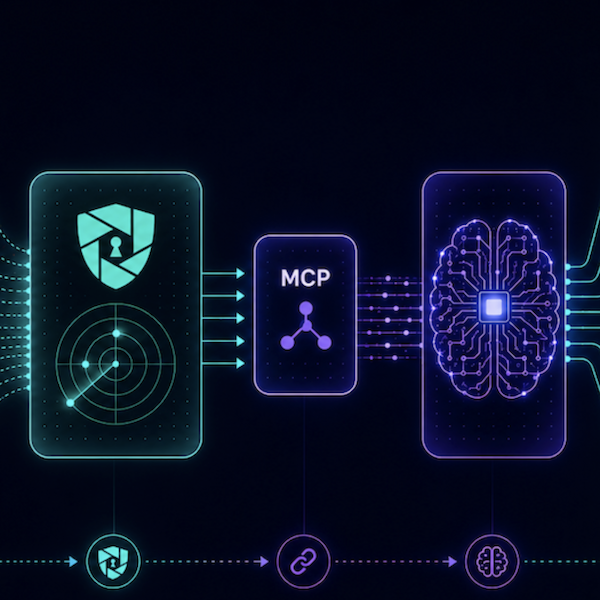
Preemptive intelligence - closing vulnerabilities faster
How to use preemptive intelligence to secure critical software as soon as it becomes known and shorten the time to action

„React2Shell“: Critical vulnerability in React & Next.js (CVE-2025-55182 / CVE-2025-66478)
„React2Shell“: Critical vulnerability in React & Next.js (CVE-2025-55182 / CVE-2025-66478) On December 3, 2025, a critical vulnerability in the React server components and the Next.js framework based on them was published. The vulnerability allows remote code execution (RCE), i.e. the execution of arbitrary code on affected servers, and potentially affects thousands of web applications worldwide. Particularly dangerous: The [...]
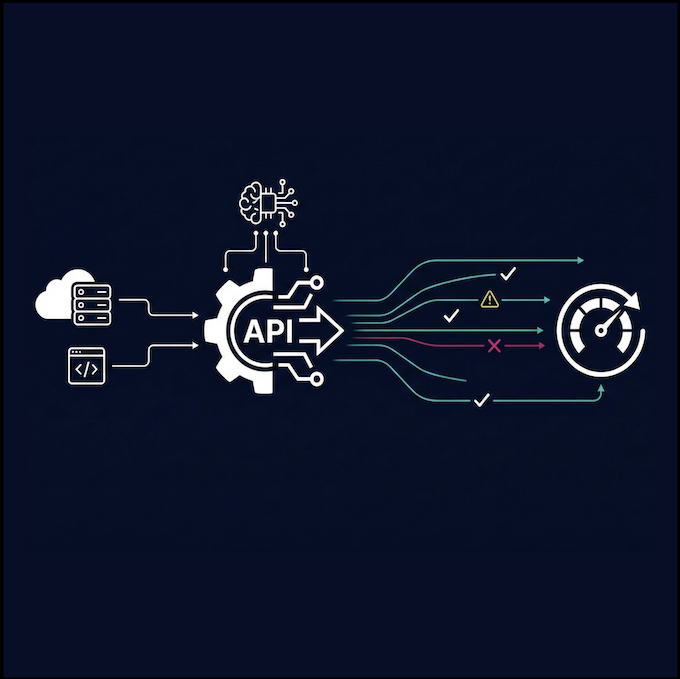
Supply chain attack on npm packages: What developers need to know
The vulnerable npm ecosystem npm is the heart of the JavaScript world. This is where developers exchange packages and build efficient applications. But it is precisely this openness that criminals are exploiting. Over 40 packages have been compromised. The attackers' goal: stealing data and manipulating build processes. The reach is particularly fatal. A single malicious package upload can affect widely dispersed projects and reduce software quality [...]

New Microsoft e-mail regulations: How to secure your business communication
The new Microsoft specifications offer the opportunity to comprehensively improve your cyber security.

LocateRisk is Best Cybersecurity Startup 2024 DACH
LocateRisk wins ATHENE Startup Award UP24@it-sa as Best Cybersecurity Startup 2024 DACH.

Excellent supplier risk management
LocateRisk awarded second place in WirtschaftsWoche's "Best of Technology Award 2024".
Supplier risk management made easy
Increase the efficiency of your supplier evaluations with automated workflows and processes.

Cybersecurity in the digital supply chain
This article provides you with an overview of the current status regarding GDPR, NIS2, DORA and CRA.